Hardware authentication transforms the sign-in experience at Rocket Casino in Australia. This method offers players enhanced security by using devices like USB tokens and biometric scanners. With the rise of cyber threats, guaranteeing account security has become paramount. As more players look for secure digital gaming spaces, the effects of this technology extend beyond mere convenience. The full effect of hardware authentication on user experience and security is yet to be fully understood.
Understanding Device Verification
While internet safety has become more important, comprehending hardware authentication is crucial for guaranteeing secure access to platforms like Rocket Casino.
Device verification involves utilizing tangible tools to verify a user’s identity, greatly enhancing safety protocols. This method frequently involves the employment of smart cards, USB keys, or fingerprint readers that necessitate physical interaction. By incorporating such tools, users can reduce the chance of unapproved entry to their profiles.
In addition, device verification can supplement traditional password methods, forming a two-step verification approach that bolsters safety. As cyber threats evolve, the use of hardware authentication becomes critical for digital sites, providing an additional level of protection against potential breaches and ensuring user confidence and confidence.
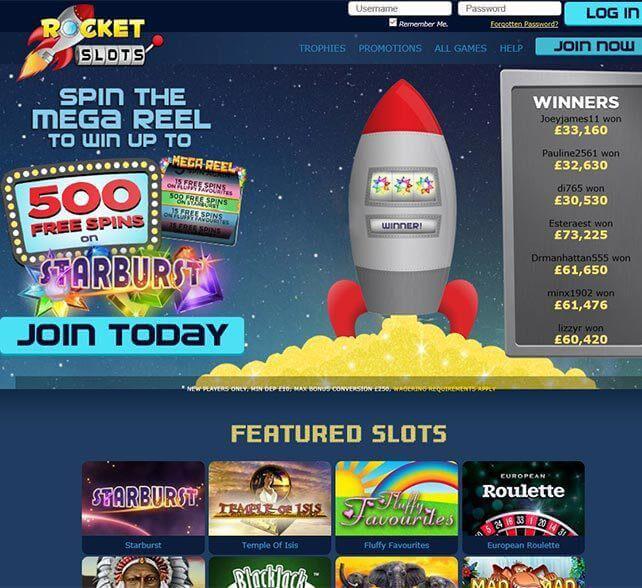
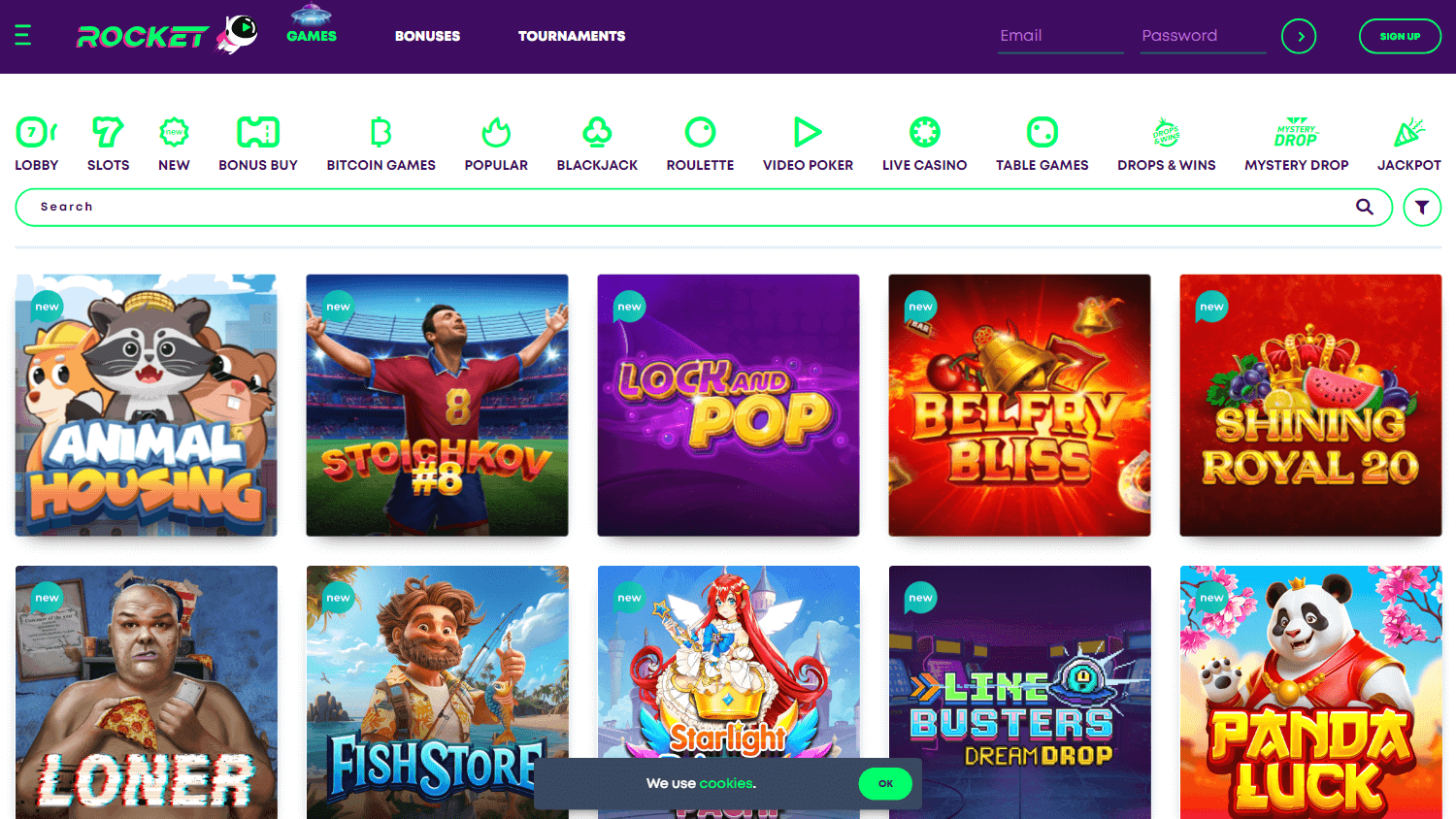
The Sign-In Procedure at Rocket Casino
As users explore the digital landscape of Rocket Casino, the sign-in procedure serves as a important step in protecting their accounts.
To enter their profiles, users must begin by visiting the official Rocket Casino site and finding the sign-in button, typically located on the main page. Upon clicking, a pop-up prompts players to enter their registered email and password.
It is essential to verify that both entries are accurate to avoid access issues. After confirmation, a successful login provides users access to their accounts, where they can discover various gaming options.
For enhanced security, frequent password updates are recommended, along with vigilance against unauthorized access, ensuring a safe and enjoyable experience at Rocket Casino.
Benefits of Hardware Authentication for Players
After efficiently going through the login process, https://rocketcasinoo.com/en-au/login/, players at Rocket Casino can improve their account security through hardware authentication. This method provides an extra layer of protection beyond traditional passwords, guaranteeing that only the legitimate account owner can access their gaming accounts.
Utilizing a physical device, such as a security key, players can greatly diminish the risk of unauthorized access and account breaches. Additionally, hardware authentication is immune to phishing attacks, as the concrete device generates unique codes required for login.
This extra complexity discourages cybercriminals, giving players confidence when engaging in online gaming. Ultimately, hardware authentication helps reinforce trust in the online gambling environment, culminating in an overall better user experience at Rocket Casino.
Ensuring Security and Privacy
How can players guarantee their security and privacy while enjoying online gaming at Rocket Casino? Players can take several preemptive measures to annualreports.com improve their safety.
Utilizing robust, unique passwords is vital, accompanied by two-factor authentication, which adds an additional layer of protection. It is suggested to confirm that the device used for accessing the casino is safe and free from malware.
Regularly updating software and applications can diminish vulnerabilities. Additionally, using a reliable virtual private network (VPN) safeguards users’ data while browsing.
Players should also review the casino’s privacy policy, comprehending how their personal information is handled. By staying watchful and informed about the latest security practices, players can guarantee a safer gaming experience at Rocket Casino.
Future of Online Gaming Security in Australia
While the scene of online gaming security in Australia continues to progress, various technological improvements are influencing the future of player protection.
Stronger encryption methods and biometric authentication are progressively being incorporated to improve user identity verification. These technologies not only safeguard personal data but also mitigate fraud risks, which are prevalent in online gaming environments.
Additionally, regulators are highlighting compliance with strict security protocols, prompting gaming platforms to embrace state-of-the-art security measures.
Artificial intelligence also serves a key role in identifying suspicious activities in real-time, further strengthening the gaming ecosystem.
As Australian players demand heightened security, the industry will certainly adapt, utilizing innovative solutions to secure a secure and enjoyable gaming experience in the years to come.
Frequently Asked Questions
Do I Need Special Hardware for Authentication at Rocket Casino?
No, special hardware is not generally required for authentication at Rocket Casino.
Users can depend on standard devices, such as computers or smartphones, featuring internet access.
Authentication processes may involve standard security measures like passwords or two-factor authentication, which can be completed through generally available software applications.
Players are urged to make sure that their devices are secure to protect their accounts but do not need additional physical authentication hardware.
Is Hardware Authentication Compatible With All Devices?
Hardware authentication is not widely compatible with all devices. Its effectiveness largely depends on the specific hardware capabilities and operating systems in use.
Most modern devices support multiple forms of hardware authentication; however, older or less sophisticated devices may lack the necessary technology.
Users should verify their device specifications and available options when considering hardware authentication solutions to confirm compatibility and optimal performance in enhancing security measures.
Can I Use Multiple Devices for Rocket Casino Login?
Yes, multiple devices can be used for logging into the platform.
Users typically have the flexibility to access their accounts across various devices such as smartphones, tablets, and computers.
However, it’s essential for them to guarantee that the login protocol crunchbase.com is followed consistently and that security measures, such as two-factor authentication if applicable, are adhered to.
This practice enhances account security while allowing convenient access across different platforms and devices.
What Happens if I Lose My Authentication Device?
If someone loses their authentication device, they would generally need to follow the service’s recovery process to regain access.
This may involve verifying their identity through other means, such as answering security questions or receiving a backup code via email or SMS.
Depending on the platform’s policies, it could take some time to restore access.
The individual should contact customer support for further assistance and guidance in re-establishing their authentication methods.
Are There Fees Associated With Hardware Authentication?
Fees associated with hardware authentication can differ depending on the service provider.
Typically, users might face initial costs for the authentication device itself, along with prospective recurring maintenance or subscription costs if relevant.
Some providers might also bill for replacements in case the device is missing or impaired.
It is advisable for individuals to examine the terms of service of their particular vendor to thoroughly grasp any prospective costs included.
About Hoteller

”Elevating Customer Journeys with Artful Care”
Book HOTEL
“Elevating experiences daily. From first touch to farewell, we blend passion and innovation to exceed expectations. Book now and indulge in enchantment. Your journey begins here.”

